Stored XSS vulnerability in hiveblockexplorer.com !! [SOLVED]
src

I was trying to understand better how Hive works at a technical level, so I was going through some documentation and exploring the content of blocks. I came across [a transaction](https://hiveblockexplorer.com/tx/8437cffaa71b2fcf292584f19ea407c6dfb40b24] that displayed the user logo at the end of the post text.
That immediately rang a bell. That image should not be there.. only text should be in that table cell!
Therefore I inspected the page and noticed that indeed some text was being parsed by the browser, meaning that it was not correctly sanitized on the server side.
I checked how the post text looked like in the hive block and I crafted a similar comment with some hidden code in it.
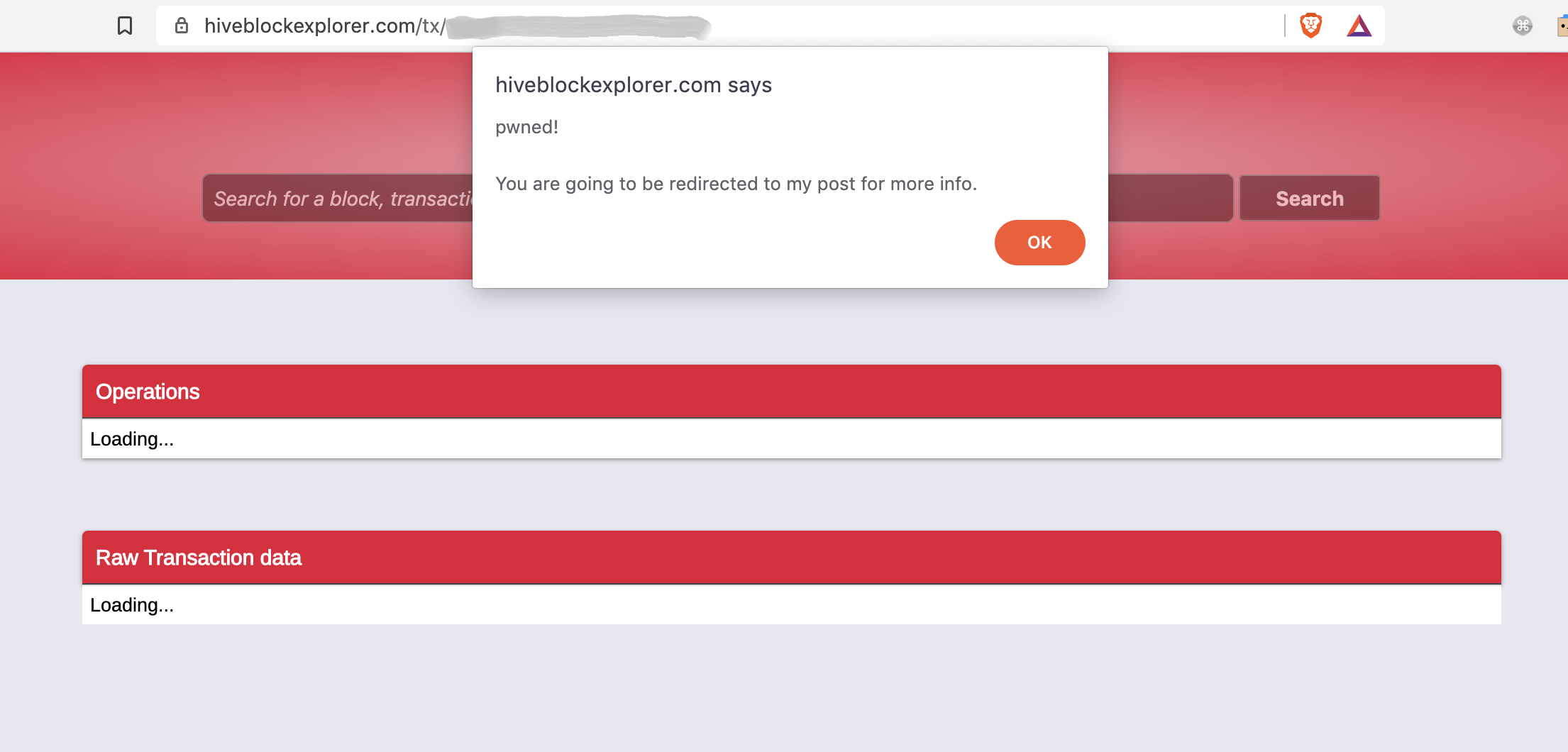
Result: I checked my new comment on hiveblockexplorer.com and the site executed my code!!
- XSS ✅
{{ for more details on what XSS is see: https://www.imperva.com/learn/application-security/cross-site-scripting-xss-attacks }}
Proof:
If you want to check yourself, I stored my harmless XSS herePS. now fixed by @penguinpablo.
If you click on that link:
You will see the alert in the screenshot above;
After 10s you will be redirected to this post of mine.
This happens because the website parses my specially crafted TEXT as code and executed it! That should never happen.
The code stored on that page could obviously be used for evil things like redirecting users to a phishing page!
A user could fall victim of it because a malicious attacker could keep spamming these type of messages into blocks OR, even worse, they could send another user a link crafted in this way as a proof of previous payment, in order to try to steal their private keys.
Guys that maintain hiveblockexplorer.com (@penguinpablo), please fix this ASAP!
Contact me on Discord if you need more details.
#xss #abuse #security #disclosure #shipit #fixasap
UPDATE 1: the same vulnerability is also on steemblockexplorer.com .. but maybe we can leave it like that there. Freaking Justin loves thieves after all..
UPDATE 2: @penguinpablo today fixed the issue: https://hive.blog/hive/@penguinpablo/qfk9ge
Good stuff!!
Domain now removed from @keys-defender blacklist.
!remove hiveblockexplorer.com
Previous security disclosures of mine:
- Malicious ads injecting code on steemit for all iOS users: https://hive.blog/steemit/@gaottantacinque/steemit-got-hacked
- Reverse tabnabbing and clickjacking: https://hive.blog/security/@gaottantacinque/steemit-chat-is-unsafe
Well done ! But please in the future contact the maintainer so he can patch the security issue before releasing it to the public. You are endangering the ecosystem by doing it that way.
True, but..
👍
PS. @howo Today I launched this, better?? 😏😏
[auto-replies to posts and comments with known compromised domains or phishing links]
https://hive.blog/hive/@keys-defender/new-feature-phishing-detection-and-auto-reply
cc: @therealwolf @saboin
Pretty cool tool !
@howo FYI - the issue is now resolved 👍
https://hive.blog/hive/@penguinpablo/qfk9ge
They don't need XSS to steal from users. People who use
Steemthese days should assume that their funds can be stolen at any moment.Very true! 🙂😌
@gtg FYI: I launched this too today and obviosly it is NOT running on Steem 😏😏
[auto-replies to posts and comments with known phishing links]
https://hive.blog/hive/@keys-defender/new-feature-phishing-detection-and-auto-reply
Found also a new XSS not yet fixxed on the same site. Messaged u on Discord.
I'm not using a discord. Come to the https://openhive.chat
You can find me (@gandalf) on #general channel or #witness or #help.
@gtg @louis88 the issue is now resolved 👍
https://hive.blog/hive/@penguinpablo/qfk9ge
Nope it's not resolved yet - just checked. @penguinpablo is not reachable on any Chat-Service so it have sent him a private memo in his wallet with Informations to the XSS i found.
@louis88
Make sure you clear your cache.
I don’t see your memo, if another field was not fixed you could send it to him encrypted with his public memo key so that only he can decrypt it with his private key.
Sure. i cleared the whole Site data in the Developer Console and opend the page where i stored the Script. And yes, i got the alert.
I have sent penguinpablo an encrypted memo on hive because he is the project owner. sure ;)
Ah, just saw it. Sent 9 hours ago 👍
https://hiveblocks.com/tx/69410f0770d8e4db4cac96a8c08d6f60eb24cd97
I just fixed this issue too.
Thank you for pointing this out.
It has been fixed. The URL below is now safe. Make sure it is not loading from your browser cache (even though it is harmless anyway).
https://www.hiveblockexplorer.com/tx/95c5b404d935cf1beba7d90bade6948f116e199e
Nice! Thanks for resolving this @penguinpablo.
Will remove hiveblockexplorer.com from my blacklist (it was temporary added until the issue was resolved).
Take care
please check your memo. i found another XSS which is also dangerous like the other.
💪
@penguinpablo Please contact me on https://openhive.chat where you can just simple Login with your Private Posting Key. I found another XSS and would like to Discuss this with you.
Thanks
@louis88
Yeh, multiple fields are affected. The server side sanitation in use in not complete.
Any update @penguinpablo please?
Hi, I can see that you are doing well here on Hive. You should try our Upvote service, we have just opened up for registration. Take a look at our lates post. We need more members. 😉
Phishing defense - test
https://hiveblockexplorer.com/tx/be9507bc8e889c0831b73d8a2045890d99b70468
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Do not click on any link on this post/comment
❗ ❗ ❗ ❗ ❗-> "https://hiveblockexplorer.com/tx/*"
More info: https://hive.blog/hive/@gaottantacinque/hiveblockexplorer-com-is-vulnerable-to-stored-xss
@keys-defender
Test passed..
🙂👍